If you have laptops floating around that have a Windows fingerprint reader, you better take a closer look at them right now.

Up until a few months ago, almost all laptop manufacturers have used the same software for their readers.
The list includes Acer, ASUS, Dell, Gateway, Lenovo, MSI, NEC, Samsung, SONY, and Toshiba.
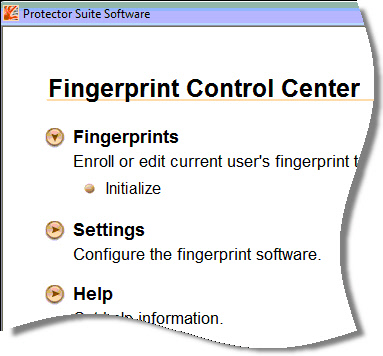
The software is called UPEK Protector Suite. It creates a password based on your fingerprint signature, and saves it as (almost) clear text in the registry. According to Elcom Soft, they used simple scrambling that can easily be reversed.
This means that if the laptop is lost or stolen, a password can be easily pulled from the laptop. This can be used to logon to your network, or decrypt files that have been encrypted by Windows EFS.
Elcom Soft has not released the details of the vulnerability, but from the information on their blog we can guess that the password is stored in one of these registry keys:
HKLM\Software\Protector Suite
HKLM\Software\Protector Suite QL
HKLM\Software\UPEK
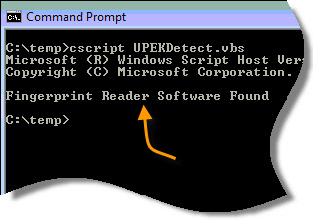
I have put together a small script that will detect if these keys are present:
Rename to .VBS after downloading.
When you run it, it will output a simple response that will tell you when the software is present:
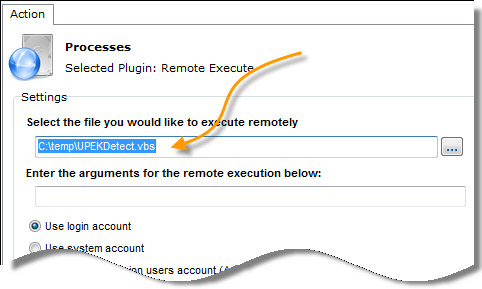
You can feed the script through the remote execute feature of Network Administrator so you can check computers remotely across your network:
Pick the script:
Easily see the responses:
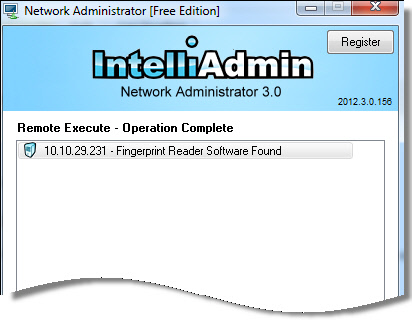
Download Network Administrator from here
Once you have identified which machines have it, it would be a good idea to uninstall the protector suite, delete those keys, and reset the password on the Windows user account used with the fingerprint reader.
UPEK was bought out by Authentec, so you should be able to get a new secure version by going to the support site for your computer.
One more thing…Subscribe to my newsletter and get 11 free network administrator tools, plus a 30 page user guide so you can get the most out of them. Click Here to get your free tools

{ 7 comments… read them below or add one }
Steve,
How do I know if I have the secure version of the fingerprint software? I have a dell laptop
Hello Jennifer,
Run the script, or you can go into Add/Remove programs and look for the UPEK software. The new version is made by Authentec, so you might want to go to the dell downloads for that laptop and get the latest fingerprint software from Authentec.
Hi Steve. Thanks for letting us know about this one. I have been so busy I did not hear about it at all – and I have quite a few laptops in the field. I will be scheduling them to come back to the office so I can take a look
Hi Steve,
Not sure if you saw this or not, not sure about an update coming anytime soon.
http://www.guardian.co.uk/technology/2012/sep/09/apple-security-iphone-5-authentec
Hi Steve,
I just bought a Samsung Q1 off of ebay and it has a fingerprint scanner, locked of course. Is there a way get into the computer as per your info.
Bill
Hi Steve
I have been using this Dell XPS M1300 for about 4 years now. Recently I had to reset the machine back to new because it had started going terribly sluggish.
At the time of installation, I activated the backup password for the UPEK Fingerprint Reader that came on the installation disk of the laptop. After finishing the installation, I tried logging in with my fingerprint swipe and it asked for the backup password that I had activated during installation. For some strange reason, it is not accepting the password that I am punching it. I am absolutely sure I am not punching in the wrong password or having the caps lock on.
I am now forced to log on only with my usual windows password. The fingerprint swipe reader is not taking me beyond the backup password query.
Is there a way to reset the password without filling in the backup password?
“Programs and Features” lists the software as “Fingerprint Reader Suite 5.6 by UPEK Inc.”
I am fully aware that your publishing an answer to this question from me can be misused by people. You may want to respond to me only on my email address instead of writing a response over here.
Thanks
Sanjay
Hi Sanjay,
I don’t have one of these readers anymore so this is just a guess…couldn’t you login the standard way as an administrator…go into user accounts, and reset the password?
Steve