We have been working hard on a new remote execution engine for Network Administrator

It really is a difficult problem to tackle with Windows 7, Vista, and 2008 in the mix. UAC, and other security features make it nearly impossible get something like this to work properly – but we have come up with some elegant solutions.
The execution engine is almost complete, but we still have some work to do before we can get it inside the latest version of Network Administrator
Why not create a free tool from this code?
What a great idea! – That is exactly what we did, and it is called ‘Remote Execute’
It allows you to take a program, and execute it remotely on any Windows 2000, XP, 2003, Windows 7, Windows 2008, or Vista machine on your network.
What makes this free tool so special? Here are some situations that it covers:
-Execute a process as the user sitting in front of the machine, not the administrator. Got a script you want to run on a machine, but as the current user? This can do the trick
-Execute in any console or remote desktop session that matches a wildcard filter. Need to run a program in Dave’s session on the terminal server? No problem
-Access to the standard input and output of the process on the remote machine. Want to have a remote command line? Remote Execute can do it.
-Mike is at the reception desk and needs a setup program launched as administrator. No need to go to his computer, just execute it as an admin in the console session. No UAC prompts either, it will be automatically elevated.
-Jennifer in accounting needs a drive mapped. Don’t want to interrupt her by remoting into her machine? Remote Execute can connect you to a command prompt that is run under Jennifer’s account. Just run the network mapping commands from your workstation and she is all set.
-Automatic detection of VBS and BAT files, so you don’t have to create a funky command line to get it to work.
Here are the command line options for Remote Execute:
RemoteExecute.exe -h [host] -u [user] -p [pass] [options] [filename] [arguments]
Options:
-h The remote host name or IP
-u Username *
-p Password *
-e Don't load users environment variables
-l Don't load users profile
-c Copy file to the remote host
-cs Run process in the console session
-n Run process as hidden
-sf [filter] Run in session where [filter] matches the user
-i Return immediately, and don't wait for it to terminate
-sa Run process under the system account
-su Run process as the session user
-q Quiet mode
* - Required options
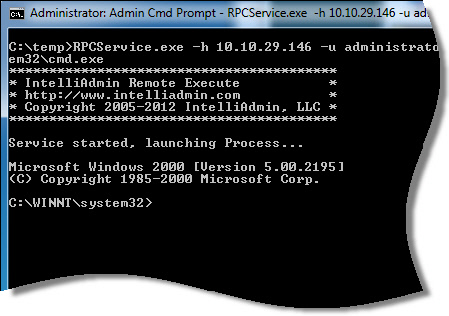
Lets start out with a simple one. You want to get a remote command line on a remote Windows 2000 machine with the IP address 10.10.10.146. What are the options to do this?
RemoteExecute.exe -h 10.10.10.146 -u administrator -p password %systemroot%\System32\cmd.exe
See, Now on my Windows 7 machine it drops down to that remote computer’s command prompt:
If you wanted to run a script as the current console user, it would look like this:
RemoteExecute.exe -su -cs -h 10.10.10.146 -u administrator -p password c:\temp\test.vbs
These two options are what enabled this to happen:
-su – Tells it to run as the current session user instead of you
-cs – Tells it to execute the application in the console session
If you wanted to copy that c:\temp\test.vbs over to the remote host, just add the -c option like this:
RemoteExecute.exe -c -su -cs -h 10.10.10.146 -u administrator -p password c:\temp\test.vbs
What about that terminal server? Lets say you have a user named mike logged into that server and want to run a script that remaps all his printers.
The command line would look like this:
RemoteExecute.exe -su -sf mike -h 10.10.10.146 -u administrator -p password c:\Code\ReMapPrn.bat
-su – This option tells it to run as mike, not the administrator. This will allow our printer mapping to directly affect his account
-sf – This is the session filter. It tells it to find the first account matching the name ‘mike’
The session filter argument can also take DOS style wildcards:
RemoteExecute.exe -sf admin* -su -h 10.10.10.146 -u administrator -p password c:\Code\BigScript.bat
Just keep in mind it will only execute on the first session that matches the wildcard.
What if you have a batch file on your local machine that you want to have copied over to the remote machine?
Just use the -c option, and it will copy the file and automatically take care of the rest:
RemoteExecute.exe -c -h 10.10.10.146 -u administrator -p password c:\Code\BigScript.bat
Make sure you always put your options first. The file you are going to execute, and its arguments always go last.
There are lots of options packed in this tool. Most of its functionality and more will be in the next release of Network Administrator, and all current customers will get this as a free update when it comes out. Buy it before the release (Towards the end of June) and get 25% off the usual price. Use the code INTE40 when ordering.
This is the first release, so please let us know if you are having trouble getting it to run a program remotely. We have tested it on every major version of Windows, but there could always be a combination of service packs and Windows version that could cause an issue. Just send an email to support@intelliadmin.com and we will get back to you asap.
Get Remote Execute from our download section
Oh – and I almost forgot. This requires file and printer sharing. Here are links on how to open this up on all major versions of Windows:
Windows XP:
http://www.intelliadmin.com/index.php/2008/12/enabling-file-and-printer-sharing-in-windows-xp/
Windows Vista, 2008:
http://www.intelliadmin.com/index.php/2008/12/enabling-file-and-printer-sharing-in-vista/
Windows 7, 2008 R2:
http://www.intelliadmin.com/index.php/2009/08/windows-7-the-admin-share/
As always, these freebies are free for commercial and personal use.
One more thing…Subscribe to my newsletter and get 11 free network administrator tools, plus a 30 page user guide so you can get the most out of them. Click Here to get your free tools

{ 23 comments… read them below or add one }
Awesome work Steve. You and your team really have done it this time. I have been using PSExec for a while, but it is starting to show its age. One issue I always run into now is if you run a process as yourself (The user account you provide on the command line) and try to push it to the console session when no one is logged in – PSExec just freezes until it times out. I tested and your tool seems to detect this, and tell me to use the system account instead. Glad that it comes back right away, but is there any way around this?
Hi Dave,
I believe this is a security issue in Windows. As it is we are in uncharted territory. If you use just standard API calls…what our program does is impossible. In the case that you describe the API call CreateProcessAsUser returns success, but no process is launched. If you dig deeper you see that CreateProcessXX actually seg faults. I believe it is a permission issue since the system account works fine.
It makes sense – I don’t think MS wants other users running processes in the console session when nobody is logged in. Would seem like a big security hole to me 🙂
True true, but then how do I run a script that uses ‘net use’. If I use the system account it does not always work properly.
The answer is don’t run it in a desktop session. With our tool just don’t use the -cs or -sf options and it will run under the service account session. The one downside with this is that the application cannot show any windows or it will cause a prompt to show up under vista/7/2008
Ahh! That is what I was doing wrong. Don’t need a visible desktop, just running a bat file silently that accesses some network shares. Thanks a ton steve.
A pro tip for the sneaky out there: If you are going to use this to get a remote command line into someones desktop, make sure you use the -n option so they don’t see a big black box on their screen from the empty command line. Here is an example of how I do it:
RemoteExecute -cs -su -n -h 10.10.10.1 -u user -p pass %systemroot%\system32\cmd.exe
That will get you a remote command line in the users desktop, and they won’t see a thing. You can launch processes, remap printers, network drives, etc. All without bothering the user but of course they need to be logged in.
Hi Steve,
This program is fantastic, it appeared just when I needed it to.
I am currently using it to deploy SCCM packages remotely using a local copy of the SCCM package instead of waiting on the replication to occur from the US to AUS.
http://youtu.be/JeuoYwXprWI
Is there any chance it could be changed so that we don’t need to specify a username and password – eg use the current logged on user.
Hi Steve,
This is a correction to my last post with an updated video.
Your RemoteExecute.exe came though just at the right time. I was looking at using Task Scheduler to install via the system account, however your utility does exactly what I was after.
http://youtu.be/0LwLQKPVSFM?hd=1
I created a tool for our support staff to allow SCCM packages to be installed straight away instead of waiting for cross domain communication to occur which increases our install times.
The application I wrote to speed up the SCCM install process does the below.
· Application queries the SCCM package directory
· Presents the packages in a live dialog
· Unzips the package to the remote machine
· Installs SCCM package using remoteexecute from IntelliAdmin
· Once completed removes the unzipped package from the remote machine
· Also has an uninstall option for the packages
Once again thank you for your wonderful tool.
Great stuff Michael. Thanks for taking the time to post. I will see what we can do about removing the user account requirement…I think it is possible since we can grab a user token from a connected pipe.
Hi Steve. Great tool! I’m very impressed. It almost meets my need… I have a service that periodically runs an executable as the console user to collect their mapped drive information. It doesn’t work with Windows 7 and I was hoping to use RemoteExecute… however the requirement for User and Password keeps it from working for me, so I too would love it if the user and password was removed (if the code is being executed against the local system as the SYSTEM user). Regardless, I know that on occasion I’ll make use of this wonderful tool as is. Thanks again.
I think it can become a great tool with some improvement.
I am trying to launch back up on Win 7 (64-bit) from Win XP (32-bit) remotely. I remotely start cmd.exe on Win 7, and when I try to run “WBADMIN START BACKUP -backupTarget:x: -include:f: -quiet”, I get a message that ‘wbadmin is not recognized as an internal or external command.’ What I find is that using remote session, I don’t find wbadmin.exe in c:\windows\system32\ while I can find the file in the folder if I personally logged in at the machine.
Hello!
If I launch a .VBS script with parameters the remoteexecute.exe strips the quote marks. this.vbs “1st par” “2nd par” -> this.vbs 1st par 2nd par
Hello,
First, love the tools! Many thanks!
I’m having problems with the free Remote Execute tool from command line. My goal is to use this for remote software installs or uninstalls. I keep getting the following:
“Connecting…
Connected, starting service…
Service started, launching Process…
Logon failure: unknown user name or bad password.”
I can’t even get it to open a command prompt:
remoteexecute.exe -h COMPUTER -u domain\me -p MyPassword %systemroot%\System32\cmd.exe
The only way it has worked is with the -su -cs switches. But this runs as the current user (not as me) so installs fail.
Thanks!
The first thing I would check to see is if the remote machine has simple file sharing enabled. When this is turned on, all authentication comes back with access denied.
Is the remote computer XP by any chance? If so check out this article for what you need to change:
http://www.intelliadmin.com/index.php/2006/01/enable-file-and-printer-sharing-on-xp-sp2/
Thanks,
Steve
Same problem.. it’s not working (at least in a domain environment).
*****************************************
* IntelliAdmin Remote Execute v1.0 *
* http://www.intelliadmin.com *
* Copyright 2005-2012 IntelliAdmin, LLC *
*****************************************
Connecting…
Connected, starting service…
Service started, launching Process…
Logon failure: unknown user name or bad password.
(Windows 7 to Windows 2008 R2)
Also it would be welcome to use current credentials instead of -u and -p
Still thanks for the effort.
I had a user with a & in the password. which threw an error as well.
I was having the domain credential issue as well, replacing domain\username with username@domain fixed it!
Hi Steve, greate tool indeed.
I have a question about the arguments usage.
RemoteExecute.exe -h [host] -u [user] -p [pass] [options] [filename] [arguments]
say I need to run
RemoteExecute.exe -h 10.10.10.1 -u user -p pass cmd /c “C:\Program Files\Some Path\First Application.exe”
How could I do that, given the intervals in both the path to the executable and in the executabe itself?
Using shortname isn’t an option.
How can you run the -h on a few machines in a text file
How do i auto run a .exe file on a remote system without me having the system IP address or username and password. I only have the email address using the computer, guide me on this asap pls
Andrew,
Sorry Andrew…not possible unless you are into illegal activities and want to send them a specialized virus via email.
Hi Steve,
Great tool. But I have a question. Is the Remote Execute network traffic encrypted?
We are worried that it does not comply with our company’s security policy that states that we must “encrypt all non-console administrative access”.
It is encrypted because at this time it does not use any of our own protocols. We are using the MS file transfer (Think copying files over your network) to send the commands.
This will change in the future when we upgrades. But if we do use our own protocol it will be encrypted.